Our BLE Locking solution is based on small low-cost modules that do not require internet and can be connected to any existing electrically operated doors, gates, barriers, elevators, etc.
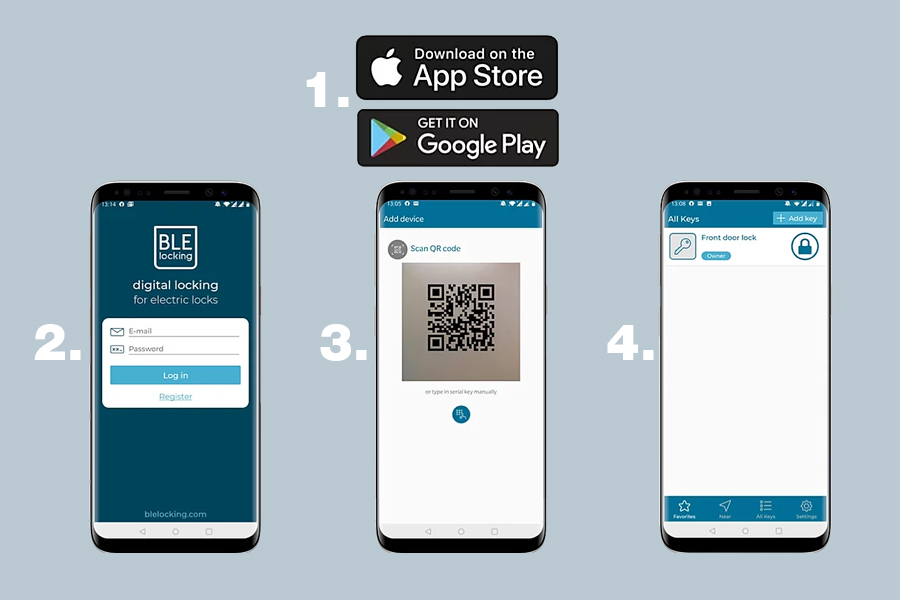
Our iOS & Android apps enable any smartphone to become a secure key. By using the app you do not need to carry with you all the physical keys, digital-key buttons, RF cards, remotes, etc.
Our BLE Locking modules and smartphone app does not require an Internet connection to function. Install the devices and download the app. After receiving your digital keys into the app you can operate the locks anywhere - even underground or in remote locations.
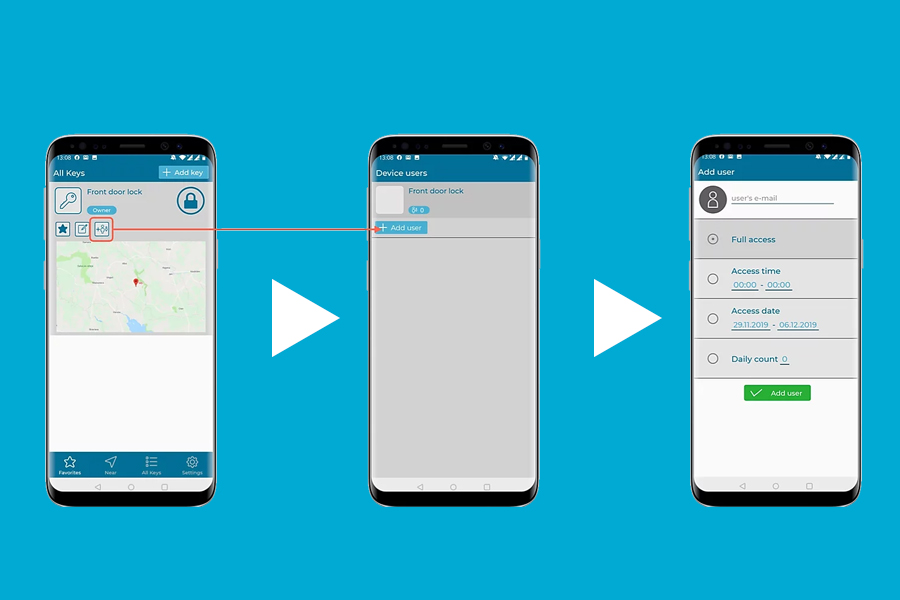
Increase access security level of your assets and property. Our solution significantly reduces risks of typical physical keys, remotes and codes that can be lost, copied, stolen or forgotten. Manage access virtually by granting or revoking access rights from the cloud. We also provide the possibility for the digital keys with different security level. You can have a key that is valid forever or you can have a key on demand, that is generated when user is on site and the key is valid for opening for short period of time, like 5 minutes for example.
Whether you have 1 door or 1000 or more, with our solution access management is a breeze. You can easily manage users, groups and their access rights right from the app or from web-based admin view.
Our API allows quick integration with your existing IT infrastructure. After integration your employees or customers can use your existing solutions and the keys with access permissions will be integrated in the background without the need to configure the permissions in separate solution.
With digital keys you will not waste money and time to order, program and distribute physical keys, remotes or cards. You have all the visibility about the usage of the keys, and you can easily grant one-time access to limited period of time. This avoids the loss caused from misused access and related incidents of theft.
BLE BROCHURE